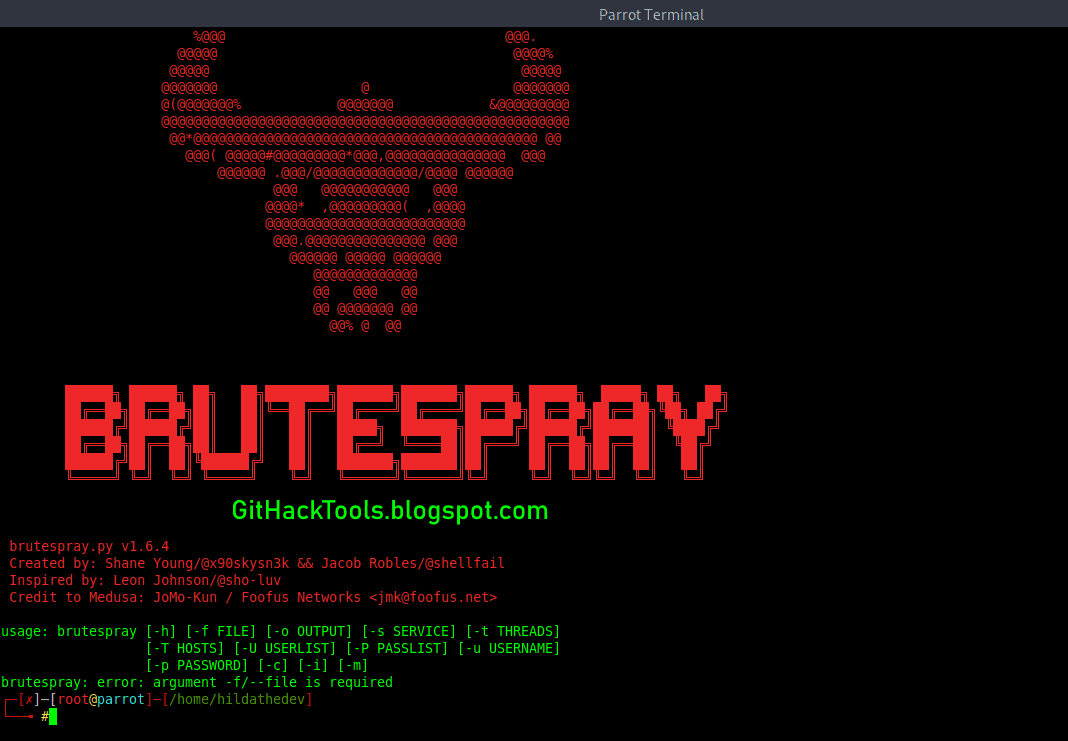
About BruteSpray: BruteSpray takes nmap GNMAP/XML output or newline seperated JSONS and automatically brute-forces services with default credentials using Medusa. BruteSpray can even find non-standard ports by using the
-sV inside Nmap.BruteSpay's Installation
With Debian users, the only thing you need to do is this command:
sudo apt install brutesprayFor Arch Linux user, you must install Medusa first:
sudo pacman -S medusaAnd then, enter these commands to install BruteSpray:
Supported Services: ssh, ftp, telnet, vnc, mssql, mysql, postgresql, rsh, imap, nntpp, canywhere, pop3, rexec, rlogin, smbnt, smtp, svn, vmauthdv, snmp.
How to use BruteSpray?
First do an Nmap scan with
-oG nmap.gnmap or -oX nmap.xml.Command:
python3 brutespray.py -hCommand:
python3 brutespray.py --file nmap.gnmapCommand:
python3 brutesrpay.py --file nmap.xmlCommand:
python3 brutespray.py --file nmap.xml -iYou can watch more details here:
Examples
Using Custom Wordlists:
python3 brutespray.py --file nmap.gnmap -U /usr/share/wordlist/user.txt -P /usr/share/wordlist/pass.txt --threads 5 --hosts 5Brute-Forcing Specific Services:
python3 brutespray.py --file nmap.gnmap --service ftp,ssh,telnet --threads 5 --hosts 5Specific Credentials:
python3 brutespray.py --file nmap.gnmap -u admin -p password --threads 5 --hosts 5Continue After Success:
python3 brutespray.py --file nmap.gnmap --threads 5 --hosts 5 -cUse Nmap XML Output:
python3 brutespray.py --file nmap.xml --threads 5 --hosts 5Use JSON Output:
python3 brutespray.py --file out.json --threads 5 --hosts 5Interactive Mode:
python3 brutespray.py --file nmap.xml -iData Specs
{"host":"127.0.0.1","port":"3306","service":"mysql"}
{"host":"127.0.0.10","port":"3306","service":"mysql"}
...Changelog: Changelog notes are available at CHANGELOG.md.
You might like these similar tools:
- BruteDum: Brute Force attacks SSH, FTP, Telnet, PostgreSQL, RDP, VNC with Hydra, Medusa and Ncrack
- FTPBruter: A FTP Server Brute forcing tool written in Python 3
- Blazy - Crack Website Logins in seconds with Bruteforce attacks
- SocialBox: A Bruteforce Attack Framework for Social Networks
- Ncrack: An High-speed Open-source Network cracking tool
- Medusa: A Speedy, Parallel And Modular Login Brute-forcing Tool


No comments:
Post a Comment